~hackernoon | Bookmarks (1972)
-
AI Tech and Its Secret Water Footprint
Also, hello! I’m Nabiha Syed, the CEO of The Markup, and I happen to be a...
-
How to Support the LGBTQ+ Youth in Crisis
The Trevor Project offers free, confidential 24/7 services to LGBTQ young people. Crisis counselors are trained...
-
CompTIA Secure Infrastructure Expert: Tips and Tricks on Security+, PenTest+, CySA+ and CASP+
The article discusses path to attaining CompTIA Secure Infrastructure Expert certifications highlighting cost-effective strategies, such as...
-
6 Skills You Need to Succeed In Cybersecurity
Cyber Security is a popular field with lots of employment options, competitive salary and a vibrant...
-
Hibernate 5 and Entities Duplication: Let’s Dive Under the Hood
Entity duplication occurs when tables are joined and multiple rows are matched. There are several methods...
-
Bitcoin Dogs Set To Make History With First Ever ICO On Bitcoin Blockchain
Bitcoin Dogs is set to be part of cryptocurrency history with the first ever ICO on...
-
How to Build an Agent With an OpenAI Assistant in Python - Part 1: Conversational
We now run a while loop to check for a completed status while handling a few...
-
States Seek Relief Against Meta for COPPA Violations
States demand relief against Meta, seeking injunctions, penalties, and restitution for COPPA violations and deceptive practices,...
-
Washington Pursues Meta for Violating Consumer Protection Act
Washington accuses Meta of unfair practices under the state's Consumer Protection Act, citing harm to consumers,...
-
Wisconsin Targets Meta Under Trade Practices Act
Wisconsin accuses Meta of deceptive trade practices, citing false representations and prioritizing profits over user safety....
-
Introducing Ola's Pre-Alpha Testnet: Empowering Data Ownership and ZK Smart Contract Innovation
Ola introduces its Incentivized Pre-Alpha Testnet, offering developers and users a glimpse into the future of...
-
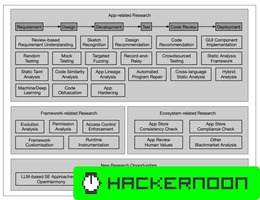
Addressing OpenHarmony Development Challenges: Insights and Solutions
This section highlights the challenges faced in OpenHarmony app development and analysis, ranging from the scarcity...
-
Software Engineering for OpenHarmony: The Research Roadmap
Discover the preliminary research roadmap for OpenHarmony, identifying software engineering gaps and proposing example works to...
-
Generate and Pray: Using SALLMS to Evaluate the Security: Conclusion & References
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
Generate and Pray: Using SALLMS to Evaluate the Security of LLM Generated Code: Related Work
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
Generate and Pray: Using SALLMS to Evaluate the Security: Limitations and Threats to the Validity
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
Generate and Pray: Using SALLMS to Evaluate the Security of LLM Generated Code: Results
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
Generate and Pray: Using SALLMS to Evaluate the Security of LLM Generated Code: Experiments
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
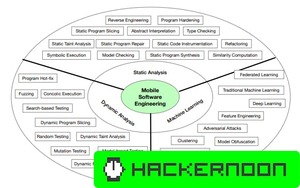
Generate and Pray: Using SALLMS to Evaluate the Security of LLM Generated Code: Our Framework: SALLM
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
Generate and Pray: Using SALLMS to Evaluate the Security of LLM: Background & Motivation
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...
-
Generate and Pray: Using SALLMS to Evaluate the Security of LLM Generated Code: Abstract & Intro
Although LLMs can help developers to be more productive, prior empirical studies have shown that LLMs...