~hackernoon | Bookmarks (1995)
-
Decoding Liquid Staking: Revolutionizing DeFi Staking with Flexibility and Rewards
Liquid staking combines the benefits of traditional Proof-of-Stake (PoS) staking with the flexibility and liquidity offered...
-
“What is Essential is Invisible;” Enter Energy/Acceleration
Techno-optimism vs. the decels
-
Exploring Nested Mapping in Solidity for Smart Contracts
Solidity nested mappings are versatile data structures that allow developers to organize and manage complex data...
-
How to Teach People to Make the Right Decisions and Delegate Important Business Tasks With no Stress
Learn how to guide your team in making profitable decisions and effectively delegate tasks. This article...
-
Financial Anti-Fraud Solutions Available on the Apache Doris Data Warehouse
Financial fraud prevention is a race against time. This post will get into details about how...
-
US Intelligence Eyes AI and Video Data for Tracking Individuals and Vehicles
IARPA is putting together a research program for the US spy community to autonomously identify, track,...
-
Insights from Davos 2024: Essential Lessons for AI Entrepreneurs in Europe
At Davos 2024, Artificial Intelligence dominated discussions, emphasizing responsible adoption, navigating regulation, promoting human-centric design, and...
-
Scaling Ethereum for the Masses: INTMAX Unveils Plasma Next
INTMAX unveils Plasma Next, a stateless layer 2 rollup that promises to take Ethereum's scalability to...
-
Lisk Partners with Indonesian Government to Empower Local Web3 Startups
Lisk announces strategic partnership with the Indonesian government's Directorate General of Informatics Applications (DGIA) The collaboration...
-
New On HackerNoon: Free Commenting For All Writers!
Writers' comments are now auto-approved, giving them control over story page discussions and seamless participation in...
-
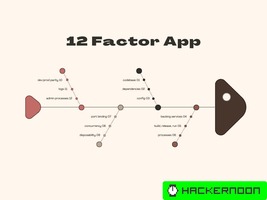
The 12 Factor App: Principles Every Cloud Developer Should Know
12 Factor Apps: What it is: A set of best practices for building cloud-native applications. Benefits:...
-
The Bitcoin Stamp Rocks Project
The creation of this unique collection is made possible through a custom algorithm developed with specific...
-
Decentralizing the AR Cloud: Blockchain's Role in Safeguarding User Privacy
The role of blockchain technology in Augmented Reality (AR) is sure to be significant, if user...
-
Either Monad: A Functional Approach to Error Handling in C#.
The article introduces the Either monad as a sophisticated tool for error handling in C#, contrasting...
-
Two Years On: How Ukraine's Cyber Warfront Is Redefining Global Cybersecurity Strategies
The Russian war against Ukraine has escalated into the most extensive use of cyber operations in...
-
Why You Should Start With a Red Test in Test-Driven Development
Kazys Račkauskas: The importance of starting with a red test. The red-green-refactor cycle is a well-known...
-
3 Contemporary CSS Techniques for Centering Items
Explore three efficient ways to center elements in CSS: Positioning, Flexbox, and CSS Grid. From the...
-
Concatenated Masked Autoencoders as Spatial-Temporal Learner: Conclusion & References
In this paper, we introduce the Concatenated Masked Autoencoders (CatMAE) as a spatial-temporal learner for self-supervised...