~hackernoon | Bookmarks (1975)
-
Python: Effective Techniques for Managing Dates in DataFrame
In data analysis and time series processing, working with date columns is essential for extracting meaningful...
-
Merging Human Cells with AI: the Future is Here
Organoid Intelligence (OI) is an advanced form of artificial intelligence leveraging engineered organoids. Organoids are miniature...
-
Takeaways From “LLM: a Survey” - Where are You Differentiating?
The LLM Survey paper serves as a really good foundation for startups to think about where...
-
Kickstarting Your GoLang Journey
Join the 100-day Go Lang challenge and dive into the fundamentals of this modern programming language....
-
UX Designer & Product Owner: 6 Tips to Up Your Collaboration
Want to improve your product owner\UX designer collaborations? Here are 6 doable tips that will help...
-
Learning WebRTC in Practice: Best Tools and Demos
The post serves as a practical guide to WebRTC, offering a compilation of tools, demos, and...
-
Reliable Messaging in Distributed Systems
Building a reliable, highly available, scalable distributed system requires adherence to specific techniques, principles, and patterns.
-
How Points System Affects Web3 Community Development & Engagement
For projects that have already issued tokens, points can help the project build a dual token...
-
How Coroutines Enable Cooperative Multitasking and Concurrency
Coroutines are a mechanism that runs a set of instructions in a cooperative way. This means...
-
The First Ola Mobile Mining App: A New ‘Verify to Earn’ Paradigm with a 10% Token Airdrop Plan
Ola’s mission with Massive is to catalyze the widespread adoption of web3, advocating for a decentralized...
-
Human Mental Health and Artificial Intelligence
This is an article that discusses ethical principles to reduce the fallacies of fear based thinking...
-
How to Master Authentication and User Flow in Node.js With Knex and Redis
Using Knex for database management, Redis for efficient caching, and Express for seamless routing. Create and...
-
Cypherpunks Write Code: Eric Hughes, Remailer and Author of "A Cypherpunk's Manifesto"
Eric Hughes, a prominent figure in the cypherpunk movement, played a pivotal role in advocating for...
-
Casting Between Types Automatically in C#
Learn about static implicit operators in C#, which enable automatic type conversions without explicit casting. Simplify...
-
Don't Build an AI Project Without Reading This First
Want to build an AI project? Learn the challenges and how to overcome them. This article...
-
How To Find a Sponsor Who Can Advocate For You
Even a great product in the market can’t sell by itself. It needs good marketing to...
-
How To Build Onboarding For Digital Products
A strong onboarding requires a deep understanding of what is that job a product gets done...
-
Why Cybersecurity for Solar Is Crucial — And Difficult
Because solar infrastructure provides essential services and is often run by government entities, it experiences a...
-
5 Spicy Product Management Takes
Five spicy takes on product management topics: roadmaps, scrum, frameworks, and more.
-
Acknowledgments and References
Explore the comprehensive list of references cited in the article, Real-time chaotic video encryption based on...
-
Advancing Video Encryption with Real-Time Parallel Computing Strategy: Conclusion
The conclusion highlights the innovative real-time video encryption strategy using parallel computing techniques, showcasing enhanced encryption...
-
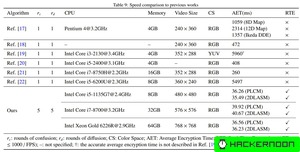
Strides in Real-Time Video Encryption: Comparison To Previous Works
The article compares the proposed real-time video encryption strategy with existing methods, highlighting its advantages such...