~hackernoon | Bookmarks (1995)
-
Cross-Border Interoperable Identity System for Developing Countries: What You Need to Know
This paper is available on arxiv under CC 4.0 license. We have identified six processes for...
-
Primary Constructors in C# 12: What They Are and Why They Are Useful
In C# 12, primary constructors play a crucial role in defining the behaviour of classes and...
-
.NET 9: LINQ Enhancements: A Detailed Introduction
The latest release of.NET 9 includes two new methods: CountBy and AggregateBy, along with the introduction...
-
Web3 : The Decentralization Dilemma: Are We Going to Be Free as Expected?
Who owns the internet? This question has multiple and endless answers that could lead to confusion....
-
Anyone Can Add Beautiful Interactive Images in ChatGPT 4 (in 30 Seconds): Here's How
Break out of ChatGPT's text-only world! With this simple trick, your chats can burst with color...
-
A Trustworthy Cross-Border Interoperable Identity System for Developing Countries: The Beginning
This paper is available on arxiv under CC 4.0 license. The authors say cross-border interoperability is...
-
Find Your Next Article Idea on HackerNoon💡
Hey Hackers! As we all know, coming up with your next big article idea can be...
-
Google's Gemini Saga: Technical Details of How the Model Misfired
Understanding all stages of Generative AI model development from pre-training, fine-tuning, safety, legal and evaluation and...
-
Cultural Intelligence in Hi-Tech Leadership: Navigating Global Business Dynamics
Cultural Intelligence (CQ) is essential for Hi-Tech Leaders to navigate communication barriers, work style differences, and...
-
The Role of Classic and Quantum Prime Patterning in Understanding Simplexity
Classical Prime Patterning and Quantum Prime Patterning; And their potential role in understanding simplexity.
-
All You Need to Know to Repatriate from AWS S3 to MinIO
Let's dig a little deeper into the costs and savings associated with repatriation to make it...
-
Web App Development Costs Are Nothing Short Of Absurd!
The exorbitant costs of web app development in this day and age are nothing short of...
-
How to Secure your Heroku Apps with SSL Certificates for Custom Domains
This guide explains how to secure your Heroku applications with SSL certificates for custom domains using...
-
The 30-Day .NET Challenge Day 3: Switch Constructs
The switch statement selects and executes a specific section of code from a list of options...
-
They Said to Use the Default Dispatchers but I Found it Was Unconfined
An explanation between the differences of using the default dispatcher in Kotlin coroutines, the Dispatchers.Default context...
-
Cypherpunks Write Code: Hal Finney, RPOW, and Bitcoin
Hal Finney, a key figure in Bitcoin's early days and a pioneer in cryptography, received the...
-
The Status Quo and Six Trends in Tokenized Government Bonds: Analyzing the Current State and Future
On-chain asset tokenization represents a long-term trend with the potential to shake up the existing financial...
-
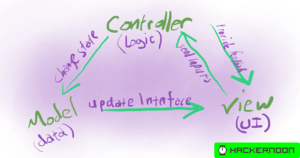
Coding Patterns Revealed
This article introduces a class-based approach for developing single-page applications (SPAs) that mirrors the efficiency of...
-
How SBINFT Plans to Revolutionize Digital Marketing With NFTs
Jangdeok Ko, the force behind SBINFT, discusses his journey from a financial engineer to founding Japan's...
-
Memecoin Rush: Avalanche's Innovative Path to Enhanced Ecosystem Liquidity
Memecoin Rush is a prize system worth a million dollars. The project was started with well-known...
-
Unlocking 2024/25: The Ultimate Guide to Top RWA Crypto Projects
Exploring Top RWA Projects for 2024/25: Insights on Maple Finance, LTO Network, and Florence Finance. This...
-
Systems Interoperability Types: The Conclusion to Our Tertiary Study
Implementing interoperability in SIS is very challenging not only in large technology-oriented systems with complicated interactions...