~hackernoon | Bookmarks (1979)
-
Optimize Planning Heuristics to Rank, not to Estimate Cost-to-Goal: Related Work
This work revisits the necessary and sufficient conditions of strictly optimally efficient heuristics for forward search...
-
Optimize Planning Heuristics to Rank, not to Estimate Cost-to-Goal: Preliminaries
This work revisits the necessary and sufficient conditions of strictly optimally efficient heuristics for forward search...
-
Optimize Planning Heuristics to Rank, not to Estimate Cost-to-Goal: Abstract & Intro
This work revisits the necessary and sufficient conditions of strictly optimally efficient heuristics for forward search...
-
Making AI Work for Your Startup: Essential Dos and Don'ts
This article delves into the essential considerations for startups venturing into AI development, emphasizing the importance...
-
Is Bulgaria a Good Option for Crypto Nomads?
There is still no separate legislation in Bulgaria that defines and regulates cryptocurrencies and the licensing...
-
Web3 Gaming and NFTs: Altura's Custom White Label Marketplace Solution
Altura is revolutionizing the possibilities of digital ownership and transaction with its industry-defined smart NFTs. Altura...
-
Unleashing the Potential of Content Creators with Whop.com
The creator economy has become a new business segment nearly representing the third-largest workforce, behind traditional...
-
LeverFi Launches OmniZK: A Secure Validation Protocol For Bitcoin DeFi And Omnichain Interactions
OmniZK is a secure validation protocol for Bitcoin that enables developers to create complex, interoperable DeFi...
-
Raiinmaker Closes $7.5M Funding To Advance Decentralized AI
Raiinmaker, a Web3 and AI Technology Company, is announcing the closing of a $7.5M seed round...
-
Sam Bankman-(Never Getting)Fried
Sam Bankman-Fried has been sentenced to a quarter of a century in prison after he and...
-
Backing Up Weaviate with MinIO S3 Buckets to Achieve Strategic Enhancement to Data Management
By bringing together the advanced vector database capabilities of Weaviate with the robust storage solutions provided...
-
Center Identity Launches Patented Passwordless Authentication For Businesses
Center Identity unveils its patented secret location authentication. The technology enables users to authenticate their identity...
-
Declaration of Independence 3.0
A decent respect to the livelihood of all mankind requires that they declare the causes which...
-
What Should I Do Today?
Feeling trapped in a rut can make you want to make a drastic change, like starting...
-
-
GMX v2 and Its Competitors: The New Wave In the Decentralized Derivatives Market And Its Impact
This article explores the changing competitive landscape in the decentralized derivatives market following the upgrade of...
-
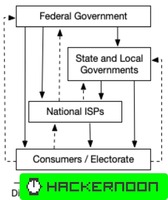
A Technical Perspective on Net Neutrality: Usage-Based Economic Models
Internet economics involve various usage-based billing structures, from bandwidth-only plans to combinations of bandwidth and data...
-
Layers of Encapsulation: Exploring the TCP/IP Model in Internet Communication
Encapsulation is a fundamental process in network communication, operating through layers in the TCP/IP model. It...
-
The Agnostic Nature of the Internet: Understanding Hardware, Network, and Content Neutrality
The Internet operates independently of hardware, network configurations, and content types, showcasing agnosticism in these aspects....
-
Net Neutrality, the Internet and the Internet Society
This section defines key terms related to the Internet and Net Neutrality, emphasizing the technical aspects...
-
A Technical Perspective on Net Neutrality
This paper provides a technical perspective on Net Neutrality, discussing Internet fundamentals, the role of ISPs,...
-
How Sound.me Simplifies AI-Powered Influencer Marketing
Sound.me is a platform for content creators and marketers. It eliminates lengthy negotiations, lack of creator...
-
Understanding Core Web Vitals: The Vital Signs of Your Website
Launched by Google in May 2020, Core Web Vitals are critical metrics for evaluating website performance,...
-
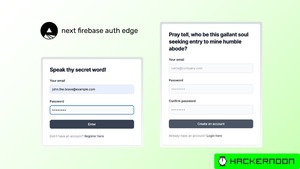
Using Firebase Authentication with the Latest Next.js Features
A comprehensive, step-by-step guide on integrating Firebase Authentication with Next.js using the zero-bundle size `next-firebase-auth-edge` library....