~hackernoon | Bookmarks (1983)
-
What's Inside Play to Earn
Deep Dive into Blockchain (EVM), NFTs, NFT Metadata Standards, Game Economies, Authorization, and How We Can...
-
Lidar Annotation is All You Need
The fusion of point cloud and image data for accurate road surface segmentation in camera images.
-
Why Integrating Low Resource Languages Into LLMs Is Essential for Responsible AI
The article explores challenges faced by low resource languages in accessing large language models (LLMs) and...
-
What Is E-Waste Hacking?
Most e-waste goes to landfills, which is damaging to the environment — and to personal security....
-
CGAAL: Wrapping It Up and What Comes Next
CGAAL is our model checker of alternating-time temporal logic properties in concurrent games. CGAAL checks such...
-
How We Evaluated CGAAL: The Experiments That We Ran
To evaluate our tool, we run several experiments. In our experiments we compare our global algorithm,...
-
A Tool Overview of CGAAL: A Distributed On-The-Fly ATL Model Checker
This paper is available on arxiv under CC 4.0 license. The syntax of the language is...
-
How CGAAL Model-Checks: A Deeper Insight
In order to check if a CGS satisfies an ATL property, CGAAL encodes the problem as...
-
How to Stitch Your Own Safety Net: Bonding Together
The Dropout Early Warning System (DEWS) assesses every incoming high schooler in Wisconsin. It issues a...
-
Getting Code Coverage Data for Each Request Coming to A Python Web Server
Code coverage is a metric used in software testing to measure the extent to which the...
-
Skynet Is Not the One You Should Be Fearing - Fear Your Favourite Car Manufacturer Instead
Xaoimi, the smartphone OEM, has entered the electric vehicle arena with the SU7 and with it,...
-
What Is Wrong With Token Rewards And How to Fix It
Token rewards have become a popular mechanism for incentivizing various behaviors. Despite their widespread adoption, token...
-
"How Many Colors Can the Human Eye See?": The Application
For instance, from this graph, we can conclude that given the same time to complete the...
-
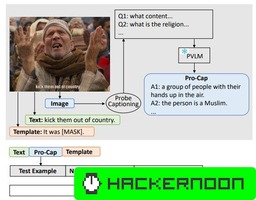
Pro-Cap: Leveraging a Frozen Vision-Language Model for Hateful Meme Detection: Appendix
This appendix provides in-depth details on implementing hateful meme detection models, insights from ablation studies, visual...
-
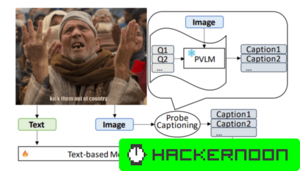
Hateful Meme Detection: Leveraging PVLMs for Zero-shot VQA Probing
This study explores using pre-trained vision-language models (PVLMs) for hateful meme detection without fine-tuning, showcasing BERT's...
-
Pro-Cap: Leveraging a Frozen Vision-Language Model for Hateful Meme Detection
Pro-Cap introduces a novel approach to hateful meme detection by utilizing frozen Vision-Language Models (PVLMs) through...
-
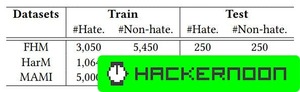
Performance Analysis of Diverse Hateful Meme Detection Datasets
We thoroughly evaluate and analyze the probing-based Pro-Cap method for hateful meme detection. Discover its performance...
-
Comparing Hateful Meme Detection Models: BERT-based vs. PromptHate with Pro-Cap
Our method uses a probing-based approach to gather critical image details essential for detecting hateful content...
-
Zero-Shot Visual Question Answering with PVLMs
This section defines the task of zero-shot visual question answering (VQA) and explores the use of...
-
Navigating the Complexity of Hateful Meme Detection
Explore various methodologies in hateful meme detection, including fine-tuning PVLMs, model ensembling, and leveraging pre-trained models...
-
Decrypting the Future: Programmable Cryptography And Its Role in Modern Tech
Programmable cryptography is still a new concept, but one that offers the chance to make very...