~hackernoon | Bookmarks (1974)
-
How David Wolf Is Building Romantic Relationships at Scale
Digi is an AI-powered chatbot that mimics the natural progression of a relationship. It aims to...
-
Learn How To Backlink Like a Pro From The HackerNoon Editors
A good set of high-quality backlinks could take a good piece to the next level. Linking...
-
How We Analyzed Crypto API Misuses in 895 GitHub Projects
The methodology involved selecting and analyzing 895 Python repositories from GitHub and 51 curated MicroPython projects....
-
Calling All Writers: Learn What The Crypto-API Writing Contest Is All About From The CoinGecko Team
In this AMA with Soon Aik Chiew and Julia Ng from CoinGecko, we discuss the Crypto-API...
-
LICMA's Analysis of Crypto API Misuses in Python Apps: Findings and Future Directions
Explore the insights from LICMA's empirical study on crypto misuses in Python applications, highlighting the impact...
-
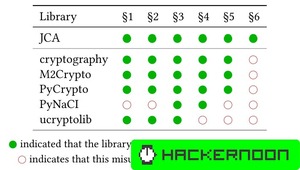
Improving Crypto API Misuse Detection: Insights from Previous Static Analysis Approaches
Previous studies have analyzed crypto misuses across various languages and platforms, including Java, Android, and C/C++....
-
Python Crypto API Misuses in the Wild: Analyzing Threats to Validity
Validity concerns in crypto misuse studies include challenges in generalization, limitations in analysis capabilities (e.g., Babelfish's...
-
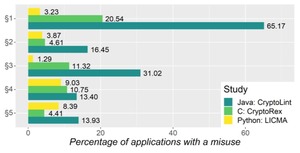
A Comparative Analysis of Crypto API Misuses Across Programming Languages
Comparative empirical studies reveal that Python's crypto libraries contribute to more secure code development compared to...
-
MicroPython Analysis: Exploring Crypto API Usage and Custom Implementations
LICMA's analysis of MicroPython reveals no crypto misuses but highlights the prevalence of custom AES implementations...
-
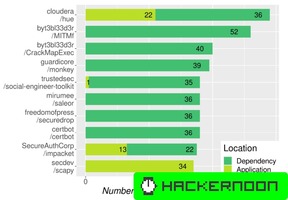
Evaluating Crypto Misuses in Python: Insights from GitHub Projects and MicroPython
LICMA's evaluation of Python projects uncovers 1,501 possible misuses attributed to 81 repositories, with 52.26% of...
-
Understanding Crypto API Misuse Patterns: A Comparative Study of Python, Java, and C/C++ Results
A meta-analysis compares crypto misuse patterns in Python, Java, and C/C++ based on studies like CryptoLint...
-
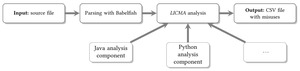
Implementing LICMA: Python and Java Analysis Components for Crypto Misuse Detection
LICMA implements crypto analysis for Python and Java, covering key crypto modules and adhering to JCA...
-
Python Crypto API Misuses in the Wild: Design and Implementation of LICMA
LICMA's design combines AST parsing, Babelfish UAST, and backward slicing algorithms to detect potential crypto misuses...
-
Addressing the Risks of Misusing Crypto Libraries
Crypto libraries often face misuse due to insecure block modes, non-random seeds, and other vulnerabilities. Understanding...
-
Common Misuses of Python Crypto APIs in the Wild
An empirical study using LICMA analyzed 895 popular Python projects and 51 MicroPython projects, finding that...
-
My Journey of Breaking into Big Tech (Or How I Ended up Joining Microsoft)
Is Big Tech all it’s cracked up to be? Are the stereotypes true? How the heck...
-
How Digital Platforms Undo Paperwork In Real Estate
In many countries, an explosive growth of remote real estate transactions occurred in 2020-2021 amidst the...
-
The Human Roots of Rising Fascism
The rise of fascism in the US and Europe is driven by deep-seated human needs for...
-
How Horizen is Redefining Blockchain with Zero-Knowledge Proofs
Explore an exclusive interview with Rob Viglione, co-founder of Horizen Labs, as he unveils the journey...
-
Interview with Dr. Yonatan Sompolinsky of Kaspa
Inclusive interview with Dr. Yonatan Sompolinsky of Kaspa, written for the book called "Kaspa: From Ghost...
-
Behavioral Interview: The Guide to Fitting In
Behavioral interviews can be daunting, particularly in the tech industry, where companies assess how well you...
-
Designing Functional Authentication and Authorization Systems
In this article, we are going to talk about a system for performing authentication and authorization...