~lobsters | Bookmarks (158)
-
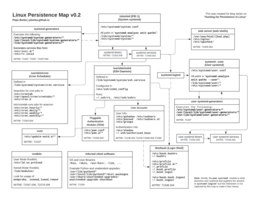
Hunting for Persistence in Linux (Part 1): Auditd, Sysmon, Osquery (and Webshells)
Welcome to this blog series “Hunting for Persistence in Linux”! This is a series that explores...
-
CHERIoT and the supply chain
Late last week we learned that much of the world narrowly avoided a backdoor in SSH,...
-
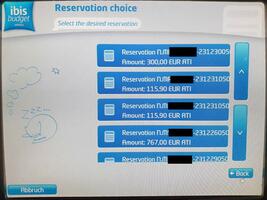
Putting an xz Backdoor Payload in a Valid RSA Key
Last week, a backdoor was discovered in xz-utils. The backdoor processes commands sent using RSA public...
-
Kobold letters – Lutra Security
Anyone who has had to deal with HTML emails on a technical level has probably reached...
-
Attacker Techniques: Gesture Jacking
A few years back, I wrote a short explainer about User Gestures, a web platform concept...