~hackernoon | Bookmarks (41)
-
Insider Threats are Increasingly Using Privilege Escalation Exploits
A new report may indicate that insider threats are finding new innovative ways to attack core...
-
Cross-Site Scripting (XSS) Vulnerabilities: Testing Strategies and Examples
XSS poses persistent threats to web apps, risking data breaches and user trust. Understanding XSS types...
-
Utilizing the Mechanics of Shamir's Secret Sharing Service — Part 2
I want to dive into SSS in a basic way and show the basic formulas for...
-
Cybersecurity Tips: Vulnerability Scanners Essentials
Vulnerability scanners like OWASP ZAP, Burp Suite, Nessus, Sn1per, Metasploit, and SQLMap are crucial for identifying...
-
Perfecting the Recipe for Robust Cloud Applications: The Barista's Approach to Shift-Left Security
# The Art of Securing Cloud Applications: A Barista's Guide. Just as each coffee bean contributes...
-
Cybersecurity Essentials: Practical Web App Security Testing Tips for QA Engineers
Practical insights and tips for enhancing web app security testing skills, focusing on vulnerabilities such as...
-
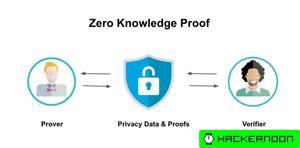
Protect Yourself From Identity Theft By Using Zero-Knowledge Proof, Solidity, and Ethereum
Identity theft can have devastating consequences for its victims, including damage to their credit, finances, and...
-
Digital Asset Protection and the Rise of Crypto Insurance
Read how crypto insurance boosts trust in blockchain, covering its types, challenges, and role in risk...
-
The U.S. Is in Desperate Need of Power Grid Modernization
The U.S. power grid is ill-prepared for resilience, causing outages, public health crises, and economic disruptions....
-
Kerberoasting Attacks Surge: CrowdStrike's 2023 Warning
Kerberos is a ticket-based authentication system. Kerberoasting is a form of assault on networks secured by...
-
Don't Make These Mistakes When Running a Phishing Simulation
Improperly run phishing simulations can make employees anxious and frustrated, and they may lose trust in...
-
The Cybersecurity Battle Has Come to Hardware
Open source collaboration enhances hardware security by allowing global contributions and constant iteration. Mature open source...
-
2023 Demonstrated How Critical Robust Authorization Really is
2023 was a year that starkly revealed the consequences of inadequate cyber security. As businesses grow...
-
Enterprise Resource Planning & Critical Infrastructure
The issues IT and Cybersecurity teams face in maintaining and protecting ERP systems, including a lack...
-
Children Should Begin Learning Cybersecurity the Moment They Switch On Their First Tablet
This article discusses the importance of introducing cybersecurity education to children at an early age, starting...